· Dayo Adetoye (PhD, C|CISO) · Partnering with the Business · 6 min read
Security Metrics That Matter:
A Governance Blueprint for the Modern Security Organization
Security is no longer just about defense - it’s about enabling business success. But without the right metrics, leaders struggle to measure impact, justify investments, and drive improvements. This blueprint cuts through the noise, providing a governance framework to track what truly matters across security strategy, operations, and tactics.

Introduction
A modern security organization must balance risk management with business enablement, ensuring that security efforts contribute positively to strategic objectives. To achieve this, organizations require a robust set of metrics that provide insights into security performance, risk exposure, and operational effectiveness. This article introduces a structured approach to governing security through a well-defined metrics framework categorized into strategic areas.
Why The Strategic Categories Matter
Our goal is to align security strategy with business objectives. However, security teams are often flooded with data but lack meaningful insights that drive decision-making. Without a structured approach, metrics become noise rather than a guide for action. The right security metrics must answer three key questions:
- Are we enabling the business while managing risk? Security should support business objectives, not obstruct them.
- Are we investing wisely? Every security dollar should contribute to measurable risk reduction and operational efficiency.
- Are we improving over time? A strong security program continuously matures, adapts, and refines its approach.
To ensure metrics serve a clear governance function, we categorize them into six strategic areas that collectively provide a holistic view of security performance. These categories help leaders move beyond compliance checklists and into proactive security management that aligns with business goals.
The categories are as follows:
- Business Enablement: Ensures security enhances business outcomes, measuring its impact on revenue and productivity.
- Fiscal Prudence: Demonstrates the optimization of security investments to reduce risk outlook: getting the most for the buck.
- Capacity: Measures the ability of security teams to proactively address long-term risks beyond day-to-day firefighting.
- Execution: Tracks efficiency, responsiveness, and effectiveness in managing security programs.
- Attack Surface: Quantifies and manages risk exposure across assets, identities, and networks.
- Maturity: Evaluates progress in adopting best practices, adhering to security compliance frameworks, and maintaining operational resilience.

Strategic Categories and Their Metrics
Let us now examine the details of each strategic category and their associated metrics:
1. Business Enablement
Business Enablement Focus
- Ensuring security enhances business growth and productivity, rather than impeding it.
- Providing insights on how security mitigates risks impacting revenue and innovation.
Key Metrics:
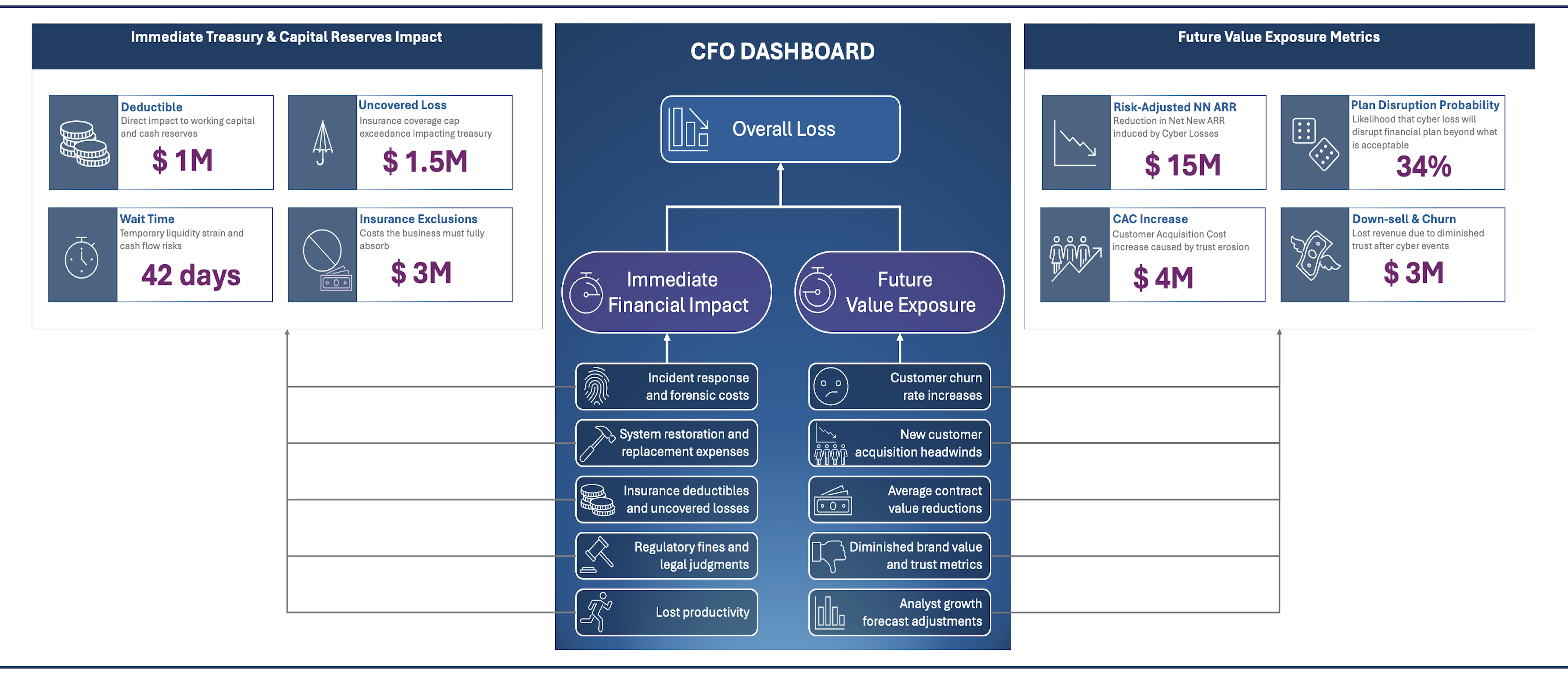
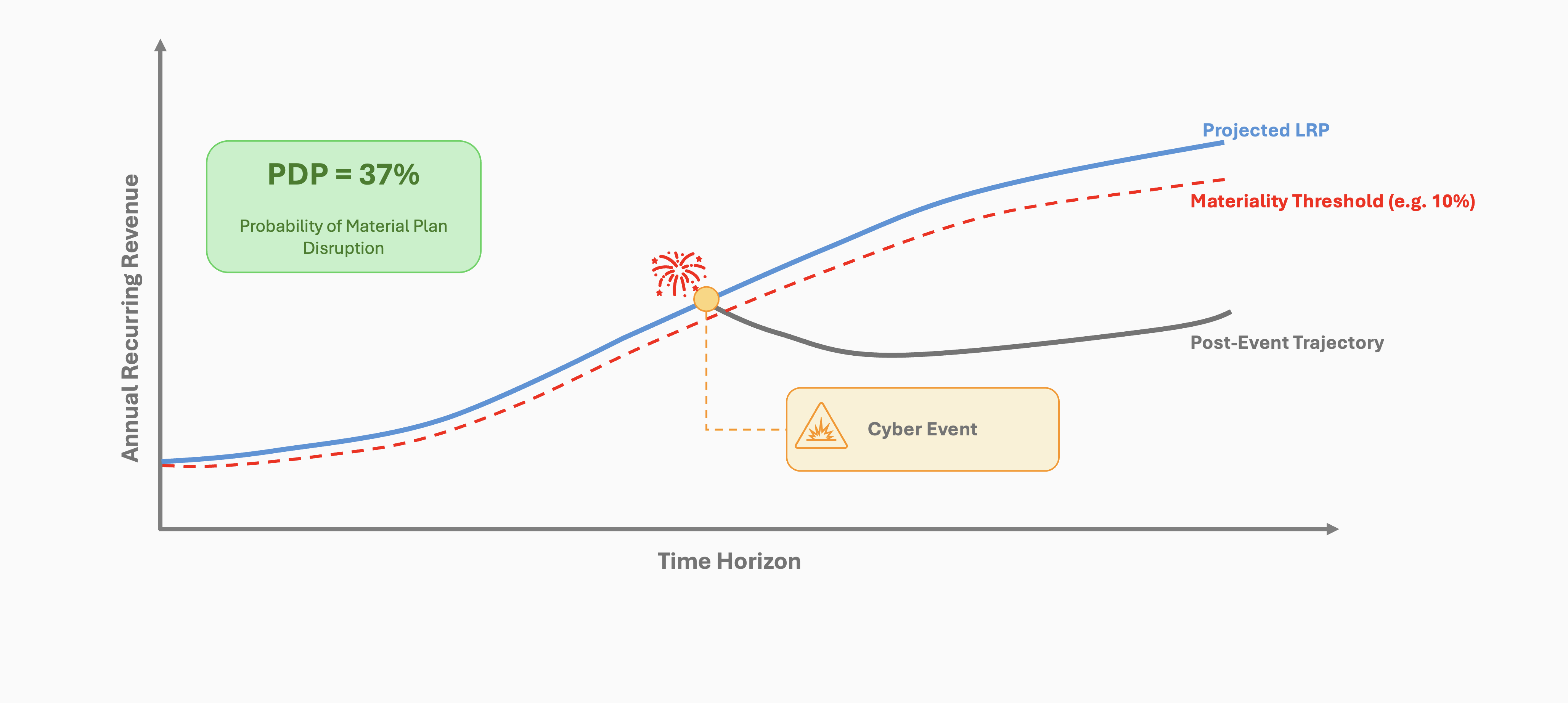
- Plan Disruption Probability (PDP): Quantifies the likelihood that cyber losses will materially impact the company’s long-range financial goals (e.g., Net New ARR or EBITDA). See PDP details here.
- Security-Enabled Productivity Improvement: Captures how security reduces friction in workflows, enabling greater business efficiency.
2. Fiscal Prudence
Fiscal Prudence Focus
- Ensuring security investments yield measurable reduction in projected risk outlook.
- Maintaining alignment between security expenditures and budgetary constraints.
Key Metrics:
- Risk-Adjusted Net-New ARR: Measures how security strategy protects net new annual recurring revenue against downside risks. See an example in the Risk-Adjusted Growth Forecast article.
- Return on Security Investment (ROSI): Evaluates risk reduction outcomes of security investments.
- Security Budget Adherence: Measures how tightly security spending tracks budgetary constraints, ensuring they align with risk appetite.
- Annual Loss Metrics (Likely, Average, Extreme): Provides financial estimates of security event impact to enable optimal resource allocation for risk mitigation.
- Annual Events Likelihood: Estimates the probability of material security events occurring allowing for decision-making to protect the treasury.
3. Capacity
Capacity Focus
- Measuring the security team’s ability to proactively manage forward-looking risks.
- Ensuring sufficient capacity to execute strategic security initiatives beyond reactive activities.
Key Metrics:
- Proactive Capacity: Measures the organization’s ability to invest in risk reduction and long-term security improvements, rather than just reacting to incidents. See an example in the Proactive Capacity Calculator article.
- Resource Allocation to Strategic Projects: Measures the proportion of resources dedicated to proactive risk reduction initiatives.
4. Execution
Execution Focus
- Evaluating the efficiency and effectiveness of security program execution.
- Ensuring operational excellence in delivering risk reduction initiatives.
Key Metrics:
- Proactive Project Completion Rate: Measures completion rates of forward-looking security projects.
- Project Delivery Success Rate: Assesses the effectiveness of delivering security initiatives.
- Time to Detect & Time to Respond: Measures the speed of incident detection and response. This includes the effectiveness of vulnerability detection and remediation processes.
- Audit Findings Closure Rate: Evaluates the efficiency of remediating audit-identified risks.
5. Attack Surface
Attack Surface Focus
- Managing and reducing the organization’s external and internal attack surfaces as a predictor of risk materialization.
- Enhancing visibility and control over exposed assets and vulnerabilities.
Key Metrics:
- Exposure Risk, Vulnerability Arrival Rates, Survival Rates, Burndown Rates: Measure how vulnerabilities and risks evolve over time.
- Top Attack Paths Control Coverage: Identifies security control effectiveness for the most critical attack paths.
- Attack Paths Testing Coverage: Measures how well attack paths are tested through simulations and assessments.
- Attack Paths with Fragile Controls: Identifies single points of failure in security controls.
- Critical Assets Controls Coverage: Assesses control coverage for high-value assets.
- Control Efficacy Trends: Tracks control performance over time. See the article on Control Efficacy for more details.
- Human Risk Score: Measures behavioral risk associated with employees, consultants, and partners. See the article on Human Risk Scoring for more details and ideas.
- Supply Chain Risk Score: Assesses the risk exposure introduced by third-party vendors and suppliers, including software and service dependencies.
- Identity, Device, Application Workload, Data, and Network Risk Scores: Provide a comprehensive view of risk across various Zero Trust security pillars.
- External Attack Surface Posture: Evaluates the exposure of the organization’s external-facing assets, with metrics coming from your external attack surface monitoring service.
6. Maturity
Maturity Focus
- Assessing the security organization’s adherence to best practices, industry standards, compliance frameworks, and good posture management.
- Ensuring continuous improvement of security capabilities.
Example Key Metrics:
- External Security Posture: Measures the maturity of the organization’s security posture in relation to external posture monitoring services.
- Breach Simulation Scores: Evaluates security capabilities and resilience based on controlled breach simulations.
- CIS Benchmark Scores: Assesses the organization’s compliance with CIS benchmarks.
- Detection and Response Maturity: Assesses the organization’s capabilities in identifying and mitigating threats.
- CISA Zero Trust Maturity: Evaluates adherence to Zero Trust principles.
- Cyber Threat Intelligence Maturity: Measures the ability to collect and act on threat intelligence.
- Threat-Informed Defense Maturity: Assesses the organization’s capability in implementing intelligence-driven defenses.
- Resilience Risk: Evaluates the ability to maintain operations despite security disruptions.
- High-Impact SaaS Posture: Measures security posture failures in SaaS applications.
Operationalizing Security Metrics for Governance
Having a structured set of metrics is only the beginning. Effective governance requires:
- Defining Ownership: Assign clear accountability for tracking and improving each metric.
- Automating Data Collection: Integrate metrics with security tools, SIEMs, and governance platforms for real-time insights.
- Setting Thresholds & Targets: Establish clear benchmarks and define thresholds for acceptable risk levels.
- Regular Reporting & Review: Implement dashboards and executive reports to track trends and drive action.
- Aligning Metrics with Business Goals: Continuously assess whether security metrics support strategic objectives and risk appetite.
Conclusion
By categorizing and operationalizing these metrics, security organizations can shift from reactive, compliance-driven approaches to proactive, business-aligned risk management. A well-governed security program not only reduces risk but also enables growth, innovation, and long-term resilience.